Machine Learning for Cybersecurity
Evolve your cyber risk strategy with advanced training in machine learning for cybersecurity from the Center for Data and Computing at the University of Chicago.
Request More Information
Many organizations now use machine learning in their operations but have not yet applied these cutting-edge approaches within traditional cybersecurity practices. Researchers at the Center for Data and Computing (CDAC) at the University of Chicago study and develop data-driven methods for applied cybersecurity, including machine learning defenses against data breaches, fraud, and other threats. From identifying backdoors in neural networks to automatically detecting malware, stolen accounts, or network attacks, machine learning offers essential new protections for businesses and individuals.
- Dates: March 30–April 27, 2021 (five weeks)
- Registration Deadline: March 23, 2021
- Live Class Sessions: Tuesdays from 7-9 PM, CT (March 30, April 6, 13, 20, and 27)
- Cost: $3,000 (Tuition support may be available. Please contact us to learn more.)
We are also able to offer participants 2.4 Continuing Education Units (CEUs) for successful completion of the program. Contact us to learn more about the eligibility requirements to earn CEUs for this program.
Designed For
This certificate is designed for a variety of professionals working across cybersecurity, applied science security, and other roles such as Information Security Managers, DevOps Engineers, Software Developers, and System Administrators
Learning Objectives
Our program is uniquely positioned to strengthen your organization’s cybersecurity measures through an advanced understanding of state-of-the-art machine learning applications. By the end of this program, learners will be able to:
- Understand basic concepts for statistical modeling, including principles for model selection for supervised and unsupervised learning tasks in the context of cybersecurity.
- Select the most appropriate models for various cybersecurity scenarios, such as malware classification, botnet detection, and intrusion detection.
- Detect and defend against adversarial attacks on machine learning models in cybersecurity settings at both training and test times.
- Identify and understand the means of navigating legal and ethical challenges that emerge from gathering data about human subjects and using it to build machine-learning models.
- Apply knowledge gained in class to real-world case studies and datasets, building both fundamental and practical expertise.
Machine Learning and Cybersecurity Course Format
This certificate is offered remotely with live online classes. Your program experience will include:
- Live Class Sessions: The primary focus of the live-online class sessions will be to discuss real-world cases and hands-on group activities.
- Weekly Self-Paced Coursework: Weekly pre-recorded lectures will be provided for all modules. The length of these recordings will be from 30 to 60 minutes long.
- Capstone Case Study: Students will have the opportunity to develop a real or hypothetical cybersecurity machine learning deployment case study, culminating in personalized UChicago faculty feedback and guidance on your strategy.
- Optional Networking and Offices Hours: Connect with peers in your industry through virtual happy hours and discuss your cybersecurity strategy with instructors through virtual office hours.
To be best prepared to succeed in this program, students should have basic familiarity with:
- Programming: Proficiency with one or more programming languages such as Python/C/C++/MATLAB/Java/JavaScript
- Basic Probability and Statistics: You should know the basics of probabilities, gaussian distributions, mean, and standard deviation
- Linear Algebra: You should be comfortable with matrix/vector notation and operations
- Computer Security: Basic knowledge of cybersecurity or applied computer security
Week 1: March 29–April 2
Class Session: March 30, 7:00–9:00 p.m. CDT
Virtual Happy Hour: 9:00–10:00 p.m. CDT
- Introduction to supervised learning models
- Logistic regression, Naive Bayes, neural networks, deep learning models
- Introduction to unsupervised learning models
- PCA, K-means, Gaussian mixture models
- Live Demonstration: Building a machine learning pipeline
Week 2: April 5–9
Class Session: April 6, 7:00–9:00 p.m. CDT
Virtual Office Hours: 9:00–10:00 p.m. CDT
- Introduction to Internet architecture, measuring Internet traffic behavior and anomaly detection
- Live Demonstration: Analyze internet network traffic using unsupervised learning techniques
- Applications of machine learning to network security
- Supervised learning examples: Spam filtering, phishing
- Unsupervised learning examples: Anomaly detection
Week 3: April 12–13
Class Session: April 13, 7:00–9:00 p.m. CDT
- Introduction to adversarial machine learning, threat models
- Example: Distorting personalization
- Defending against adversaries
- Example: Evading intrusion/attack detection
Week 4: April 19–23
Class Session: April 20, 7:00–9:00 p.m. CDT
- Fairness, Transparency, and Explainability in cybersecurity ML models
- Privacy definitions and how to actualize privacy for cybersecurity applications in industry
- Externalities and implications of errors in ML models for cybersecurity
- Responsible data lifecycles
- Hands-on lab focused on building a model to detect fraudulent accounts leveraging virtual case study
Week 5: April 26–30
Class Session: April 27, 7:00–9:00 p.m. CDT
- Students have the option to develop a real or hypothetical cybersecurity machine learning deployment case study, culminating in personalized UChicago faculty feedback and guidance on your strategy.

Actionable Frameworks
Develop a holistic approach to data science focused on foundational topics that can be applied to new and evolving situations across cyber risk management.
Real-world Context
Apply foundational techniques to contemporary case studies, complex datasets, and unique business challenges.
Engage with Experts
Learn from and network with leading faculty and colleagues across the science and technology sectors.
Meet the Faculty
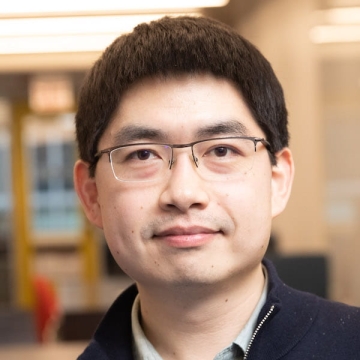
Yuxin Chen
Assistant Professor, Department of Computer Science
Yuxin Chen is an assistant professor at the Department of Computer Science at the University of Chicago. Previously, he was a postdoctoral scholar in Computing and Mathematical Sciences at Caltech, hosted by Prof. Yisong Yue. He received his PhD degree in Computer Science from ETH Zurich, under the...

Blase Ur
Neubauer Family Assistant Professor of Computer Science and the College
Blase Ur researches computer security, privacy and human-computer interaction. His focus is on helping users make better security and privacy decisions, and improving user experience within complex computer systems. Asst. Prof. Ur founded the UChicago SUPERgroup, an interdisciplinary research...
About the Center for Data and Computing
The Center for Data and Computing is an intellectual hub and incubator for data science and artificial intelligence research at the University of Chicago. CDAC catalyzes new discoveries by fusing fundamental and applied research with real-world applications. As the focal point for data science research on campus, CDAC engages leaders from industry, government, and academia through innovative events and partnerships to spark new collaborations and technological discoveries.
