Articles
Articles and stories on timely topics and trends across a variety of industries.
Leadership Unscripted
The Second City improv techniques protecting brands in crisis.
Brand Resilience: Crisis Communication for Senior Leaders
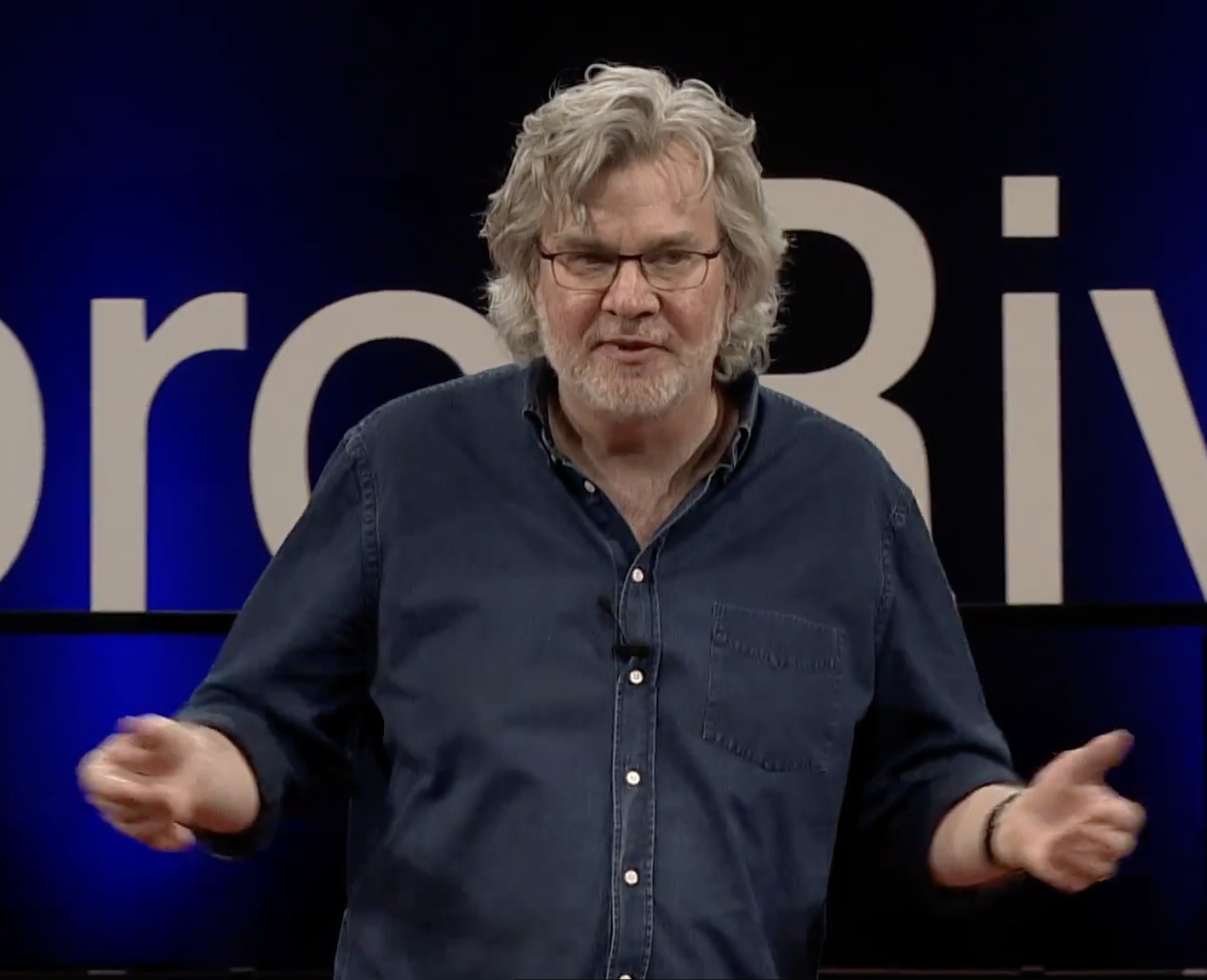
Leadership Unscripted
The Second City improv techniques protecting brands in crisis.
Read time – 6 minutes

Connecting Science with Compliance
Morayo Adebiyi-Uchendu, PhD, Regulatory Writing
Read time – 4 minutes
Editing Careers in the Digital Age
A certificate program shows how learning editing fundamentals opens doors to unexpected futures.
Read time – 5 minutes

Winning the Numbers Game
Helen Armalas, Editing certificate
Read time – 4 minutes

Reinvigorating Regional Media
Liz Long, Editing certificate
Read time – 3 minutes

The Art of Legal Precision: Why Lawyers Need to Learn to Edit
Shape narrative and craft arguments that are both engaging and tightly reasoned while using core editing and AI skills.
Read time – 4 minutes
Leading with Clarity When the Ground Won’t Stop Shifting
Crisis business communication to protect your brand and lead your people.
Read time – 5 minutes

Clear Words, Better Care
How CME credits for communication skills are expanding what it means to practice medicine.
Read time – 4 minutes

Expanding Expertise: From Lab Bench to Freelance Success
Nicole Cotroneo, Medical Writing and Editing and Regulatory Writing certificates
Read time – 5 minutes

Decoding Regulation: Clarity Across the Compliance Landscape
Leah Carter, Regulatory Writing instructor
Read time – 4 minutes